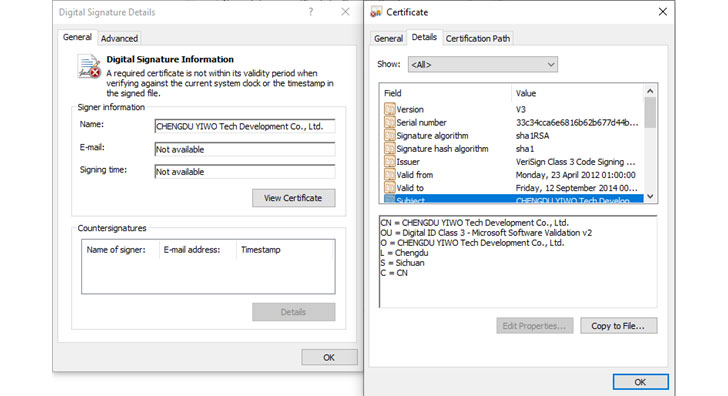
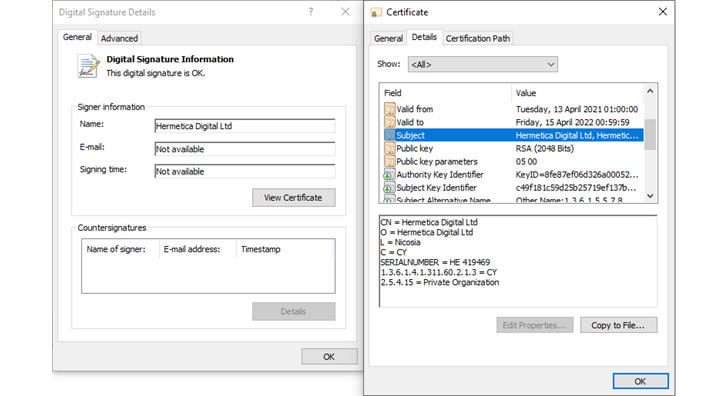
As Russian forces formally launched a full-scale military operation against Ukraine, cybersecurity firms ESET and Broadcom’s Symantec said they discovered a new data wiper malware used in fresh attacks against hundreds of machines. The wiper was dubbed “HermeticWiper” (aka KillDisk.NCV) by the Slovak company, and one of the malware samples was compiled on December 28, 2021, implying that the attacks had been planned for nearly two months. In a series of tweets, ESET stated, “The wiper binary is signed using a code signing certificate issued to Hermetica Digital Ltd.” “To corrupt data, the wiper exploits legitimate drivers from the EaseUS Partition Master software. The wiper then reboots [the] computer as a final step.”
HermeticWiper is delivered via the benign but signed EaseUS partition management driver, which then corrupts the first 512 bytes of every physical drive’s Master Boot Record (MBR) before triggering a system shutdown and effectively rendering the machine inoperable. In a report analyzing the new malware, SentinelOne’s principal threat researcher Juan Andres Guerrero-Saade said, “After a week of defacements and increasing DDoS attacks, the proliferation of sabotage operations through wiper malware is an expected and regrettable escalation.” At least one of the intrusions involved the attackers deploying malware directly from the Windows domain controller, implying that they had gained control of the target network.
The scope and impact of the data-wiping attacks, as well as the identity of the threat actor behind the infections, are still unknown. However, following the WhisperGate operation in mid-January, this is the second time this year that destructive malware has been deployed on Ukrainian computer systems. The wiper attacks come after a third “massive” wave of distributed denial-of-service (DDoS) attacks on Wednesday, which knocked out online portals for the Ministry of Foreign Affairs, the Cabinet of Ministers, and the Rada, Ukraine’s parliament.
The outages of two of the largest Ukrainian banks, PrivatBank and Oschadbank, as well as the websites of the Ukrainian Ministry of Defense and the Armed Forces, were caused by a DDoS attack from unknown actors last week, prompting the UK and US governments to blame the Russian Main Intelligence Directorate (GRU), which the Kremlin has denied.
DDoS attacks send torrents of junk traffic at targets in order to overwhelm them and make them inaccessible. The CERT-UA later discovered that the February 15 incidents were carried out by leveraging compromised MikroTik routers and other IoT devices, and that they were carried out using botnets such as Mirai and Mris.
Furthermore, 121 cyber attacks targeting information systems belonging to Ukraine’s state institutions are said to have been unsuccessful in January 2022 alone.
That’s not all, though. According to a report released earlier this week by Accenture, cybercriminals on the dark web are looking to profit from the ongoing political tensions by advertising databases and network accesses containing information on Ukrainian citizens and critical infrastructure entities on RaidForums and Free Civilian marketplaces in the “hopes of gaining high profits.”
Since the beginning of the year, a steady stream of disruptive malicious cyber acts has prompted the Ukrainian law enforcement authorities to characterize the attacks as an attempt to sow fear, erode trust in the state’s ability to protect its citizens, and destabilize the country’s unity.
On February 14, the Security Service of Ukraine (SSU) stated, “Ukraine is facing attempts to systematically sow panic, spread false information, and distort the true state of affairs.” “When all of this comes together, it’s just another massive wave of hybrid warfare.”